 OWASP had released a X-Mas Capture the Flag challenge. This challenge was the 7th challenge for the OWASP AppSec Research 2010 in Stockholm, Sweden. The winner gets the free entrance to their next year's conference.
OWASP had released a X-Mas Capture the Flag challenge. This challenge was the 7th challenge for the OWASP AppSec Research 2010 in Stockholm, Sweden. The winner gets the free entrance to their next year's conference.Before you start hacking away, please read the rules first.
Rules of the Challenge:
- Please do not perform any resource-intensive tests, as the machine is pretty low-end and can be DoS:ed without much effort.
- The computer at the given IP address is the only system involved in this challenge, so please do not perform any tests of neighboring systems.
- Otherwise, you are free to hack away!
The Challenge URL: 66.249.7.26

For more infomation on the challenge, visit OWASP AppSec Research 2010
Updated on 24 Dec
Have some free time yesterday and decided to try out on the challenge.
I run a simple port scan on the IP and found port 22 and 80 running. So i tested the port 22 with SSH and HTTP. No respond from it.
Planning to run a Vulnerability scan on the webserver. But do not want to trigger the IDS in my office. So i move on to check the source code of the webpage. The source code looks like a static HTML page without any input fields. But the programmer did provide some pointer to us.
Congratulations, you reached the first goal. You checked the source! Now,
go ahead on your quest for the christmas spirit.
Join us inside the merry box and find the hidden present! And dont forget to leave
milk and cookies for santa and his helpers.
* Rule#1 : Do not (D)DoS this machine, it is a very very fragile old christmasgnome
who will topple if you push him too hard.
* Rule#2 : No more rules.
Try to search for any other folders on the website. Tried several folder such as /help/, /admin/, /cgi/, /bin/, /samples/, etc.. Manage to detect /icons/ and /manual/. There isn't anything useful in those folder.
While reading through the pointer from the source code again, i notice something they are trying to tell us. The statement "dont forget to leave milk and cookies for santa and his helpers.". The word cookies maybe relavant. So decide to try adding cookie on the request.
When using the "Cookie: testing", the webpage returns "Noooo noooo noooo - but close!". So it seems i am on the right track and the input to this webpage is via cookie.

So i decide to try changing the cookie values to "christmas", "merry", "present", "milk", etc.. It still return with "Noooo noooo noooo - but close!". Only when i use "santa", it returns with something positive. It show "Hoooo hoooo hoooo" with a long code "YToxOntzOjE5OiJCRU5DSE1BUksoMSxNRDUoMSkpIjtzOjE6IjAiO30=" . It looks like some hashing or encoding.

After checking on various hashing and encoding format, the code was found to be using Base64. It was decoded as "a:1:{s:19:"BENCHMARK(1,MD5(1))";s:1:"0";}"
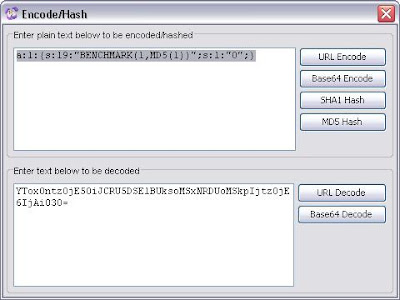
Not knowing what to do with it, i try add it in the header and the body of the request. But it don't seems to work. So i continue to work on other cookie input. With some experience studying cookies from Ads site such as yieldmanager and doubleclick, i decided to give values to the "santa" variable.
I try putting "santa=1", "2" and "3". It seems to return different codes. So it means that the webpage is accepting the values and output according to the input. Maybe there are some calculation or algorithm in the program.

When i try with a large numbers like "santa=123456789", it gives an ouput "Ouch! Too much eggnog". Seems that there is a limit to the input values.

When i try with a string values such as "santa=testing", it gives an error "Warning: mysql_fetch_assoc(): supplied argument is not a valid MySQL result resource in /var/www/xmas/frontend/index.php on line 95". Looks like there is a MySQL database running in backend and the challenge will likely to be using SQL injection.

After collecting several encoded codes and trying out various different inputs (code injection). I am more or less stuck on this challenge. But i notice that a hint pops up saying "The magic parenthesis of Antiochia!", when i was trying various inputs and refreshing the webpage.

Frankly, i am not good in programming and not sure what this code or function "a:1:{s:19:"BENCHMARK(1,MD5(1))";s:1:"0";}" represents? And also not sure about the hint of "The magic parenthesis of Antiochia!", maybe it is about using parenthesis in the injection. See if anyone can pick up and solve the "mystery". I will be out of town to enjoy my holiday this christmas weekend. That's all from me on this challenge.
Merry Christmas!!

1 comment:
Good finding. Merry Xmas
Post a Comment